The nastiness just keeps getting worse.
Macs have joined the ransomware party, Petya gives us a new twist on an old attack, and now ransomware targets hospitals. On top of that, the US and Canadian authorities have issued a joint cyber alert that things are only going to get worse.
Mac Ransomware
It is rather dated news by now, but it is still significant to recognize that “First Mac ransomware spotted” out in the wild. Mac OS X users can no longer afford the complacency of not being a target by malware writers. This explodes the myth, and it has always been a myth, that “Macs don’t catch viruses.”
Petya: A New Twist on Boot Sector Viruses
Back in the day, when floppy disks were king, viruses were often spread via “sneaker net”. Someone would stick an infected floppy into a machine, and BOOM! the computer was infected. Later, along would come some unwitting person who would stick their floppy into the infected computer, get their floppy disk infected and start the cycle all over again.
The worst were boot sector viruses. They would infect the boot sector of a disk and take control of the computer before the operating system even had a chance to do anything. It was so common in the computer lab that we wrote a script that would fdisk, format and reinstall Windows 3.1 once a day. There wasn’t much we could do about the floppies running around (except hope the stupid antivirus would stop it, which it rarely did), but at least we could ensure our machines were clean at the beginning of the day.
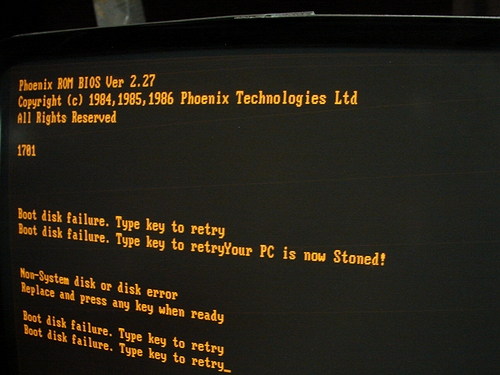
Now, Petya can do this without a floppy, it appears. Worse, it infects it with ransomware! At least the stoned virus could be fixed with a new MBR.
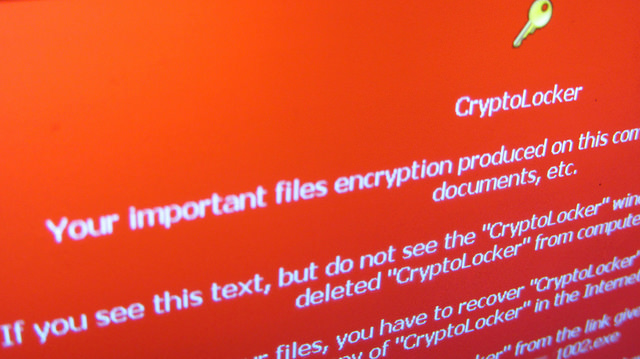
“Petya – Taking Ransomware To The Low Level” points out that the malware uses a two-pass method. First, it encrypts your boot sector, and then it reboots and encrypts much but not all of your files on your hard drive. It causes a BSOD, which is stage 1 where the malware dropper infects the MBR. If you shut it off at this point, your hard drive can be saved because it has not yet infected your files.
It is spread by emails claiming to be a job applicant. When you open the “CV”, the first tip-off should be that the UAC asks if you want to allow the program to make changes to your system. If the user clicks on Yes, the system is now infected.
New Malware MSIL/Samas.A Targets Hospitals
A new low, even for malware writers, is one that infects JBOSS servers in order to launch encryption of network shares. It is a new low because they seem to be targeting hospitals, according to “Ransomware Takes Nasty New Twist“.
According to the article, it can shut down entire networks. The ransomware then offers to decrypt the local PC for a set price or decrypt the files for all at a bulk price.
I doubt that modern medicine can yet effectively combat the common computer virus.
Cyber Alert
It appears that ransomware is on the rise, and apparently US and Canadian authorities agree, according to “Ransomware alert issued by US and Canada following recent attacks“.
Every week seems to bring news of another case of ransomware.
It’s nasty stuff. Nasty enough that the US and Canada on Thursday issued a rare joint cyber alert warning about the recent surge in ransomware attacks, in which data is encrypted and crooks demand payment for it to be unlocked.
Better lock those systems down!

Perspecsys Photos by CCA-SA
Bonus: Malware Sends Speeding Tickets
Here is one I have trouble believing. If it weren’t being reported by some reputable rags like Wired in “Security News This Week: Clever Malware Is Sending People Fake Speeding Tickets“, I would be tempted to think it was an April Fool’s joke.
The malware infects a user’s smartphone, and then it can use the GPS to determine when and where they are speeding. The user will then get an email stating they were speeding and to click on a link to see the details. The link naturally goes to a phishing site.
What makes it particularly hard to swallow is the claim by some, including Geek News Central that it includes a pic of the license plate. Say, what? This claim is so over the top that I definitely would have to see it to believe it.
It turns out this is misreading the news, however. According to The Verge article “Malware scam appears to use GPS data to catch speeding Pennsylvania drivers“, the link purports to go to details about the speeding including a picture of the license plate.
